.avif)

Secure everything, Compromise nothing.
Secure your code, cloud, and runtime in one central system.
Find and fix vulnerabilities automatically.





















Aikido - All in one Security platform
Code (ASPM)
Cloud (CSPM)
Test (Domains & API)
Unified Platform
Sure, you can juggle multiple security tools.
Each with their own pricing, alerts, and opinions.
Most of them operate in isolation and miss what actually matters.

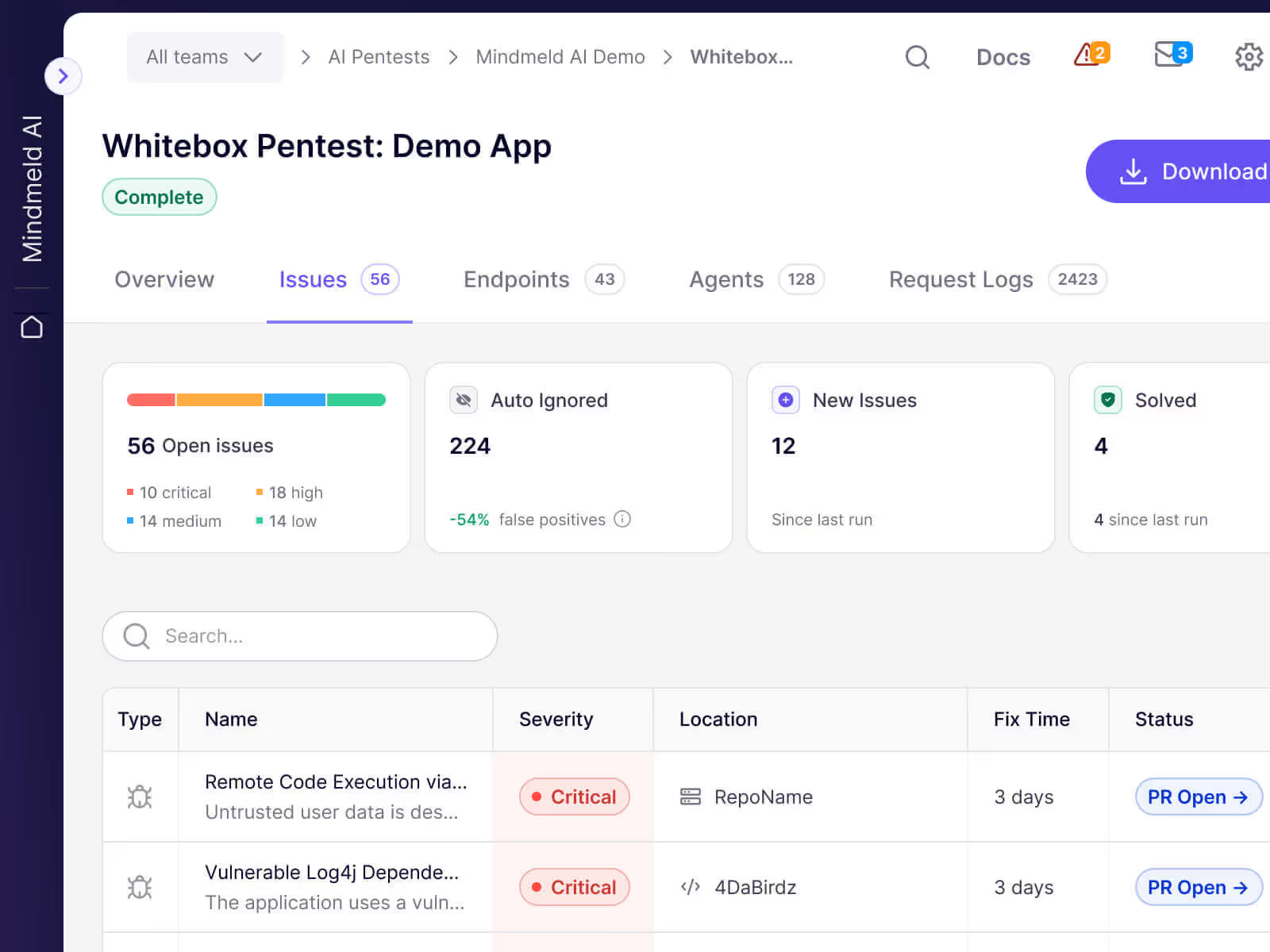
Pentests
Get a pentest done in hours. 200+ agents unleashed that outperform humans every single time. No High+ finding? Money back.

Replaces

Open source dependency scanning (SCA)
Continuously monitors your code for known vulnerabilities, CVEs and other risks or generate SBOMs.

Replaces


Cloud posture management (CSPM)
Detects cloud infrastructure risks (misconfigurations, VMs, Container images) across major cloud providers.

Replaces

Static code analysis (SAST)
Scans your source code for security risks before an issue can be merged.

Replaces



Surface monitoring (DAST)
Dynamically tests your web app’s front-end & APIs to find vulnerabilities through simulated attacks.

Replaces


Infrastructure as code scanning (IaC)
Scans Terraform, CloudFormation & Kubernetes infrastructure-as-code for misconfigurations.

Replaces

Container image scanning
Scans your container OS for packages with security issues.

Replaces


Open source license scanning
Monitors your licenses for risks such as dual licensing, restrictive terms, bad reputation, etc..

Replaces


Malware detection in dependencies
Prevents malicious packages from infiltrating your software supply chain. Powered by Aikido Intel.

Replaces

Outdated Software
Checks if any frameworks & runtimes you are using are no longer maintained.

Replaces

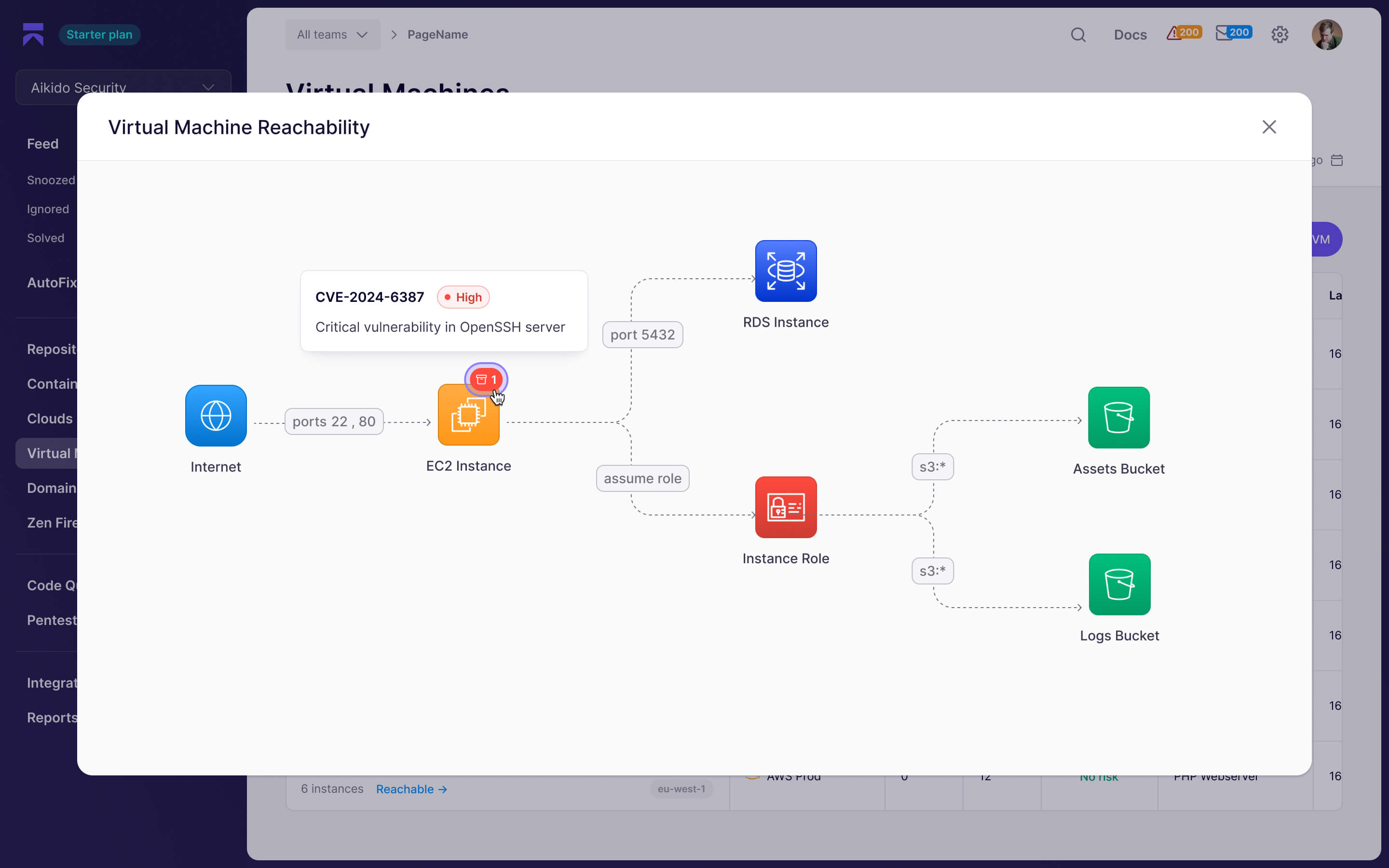
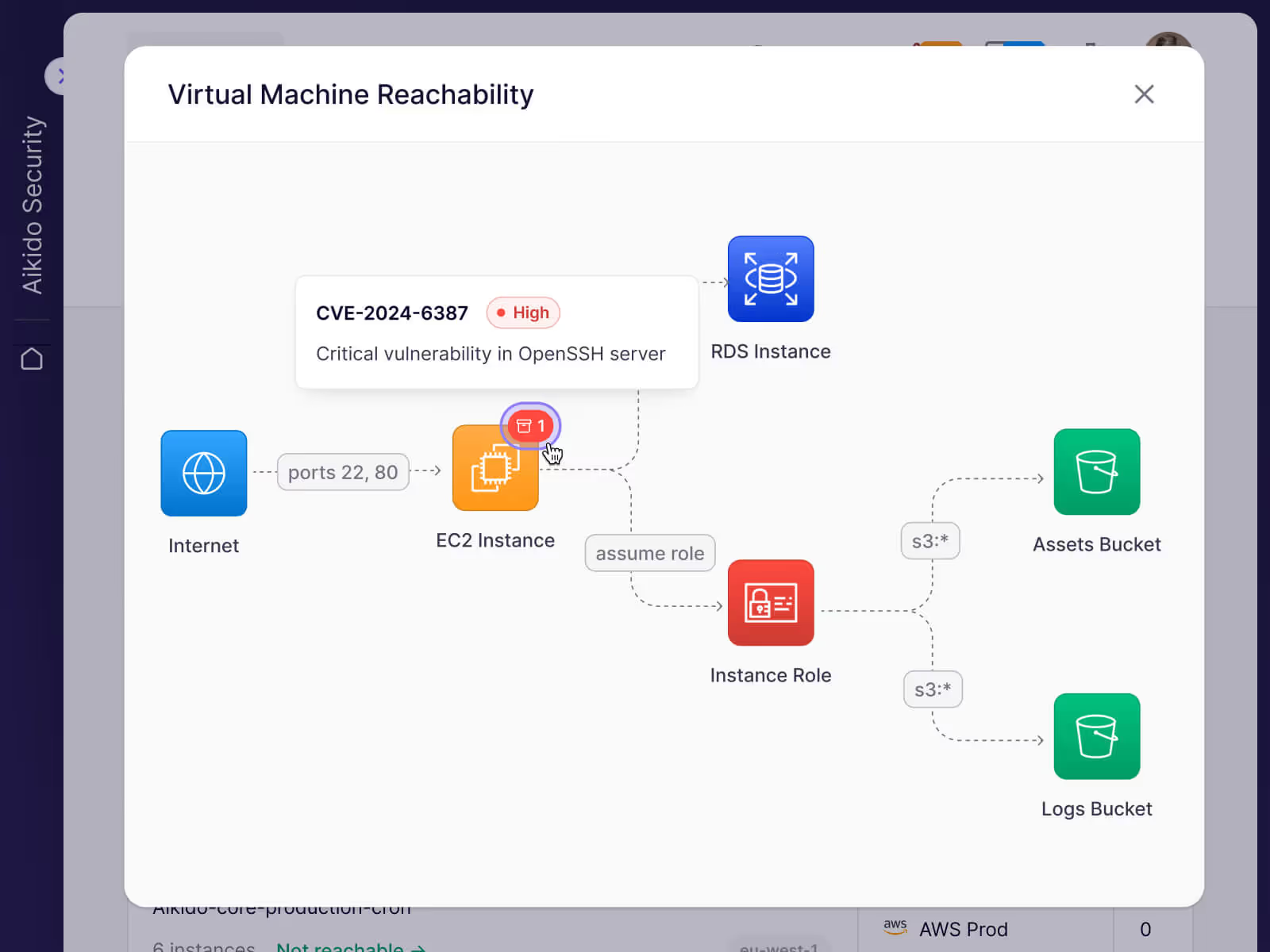
Virtual Machine Scanning
Scans your virtual machines for vulnerable packages, outdated runtimes and risky licenses.

Replaces

Kubernetes Runtime Security
Identify vulnerable images, see the impacted containers, assess their reachability.

Replaces


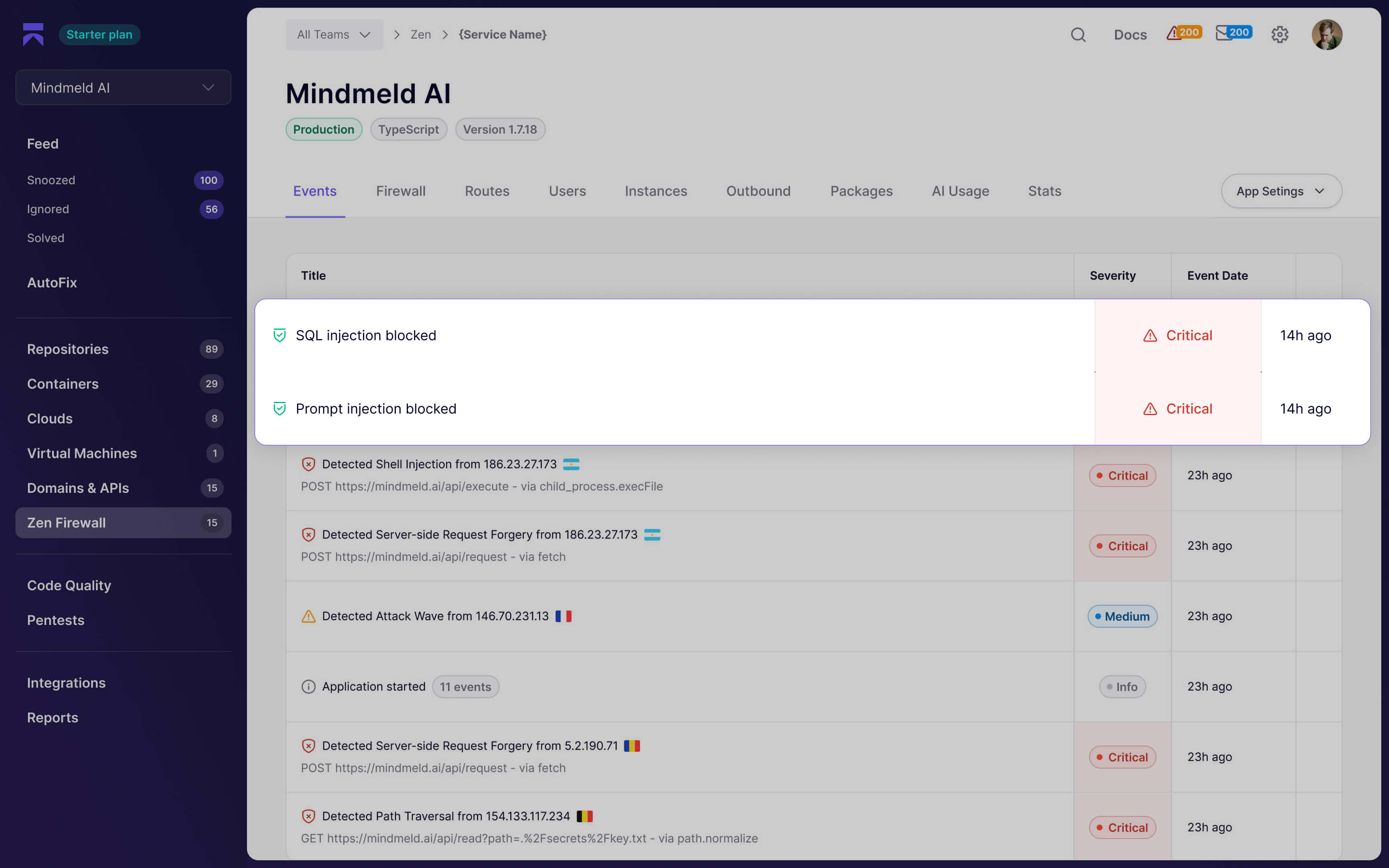
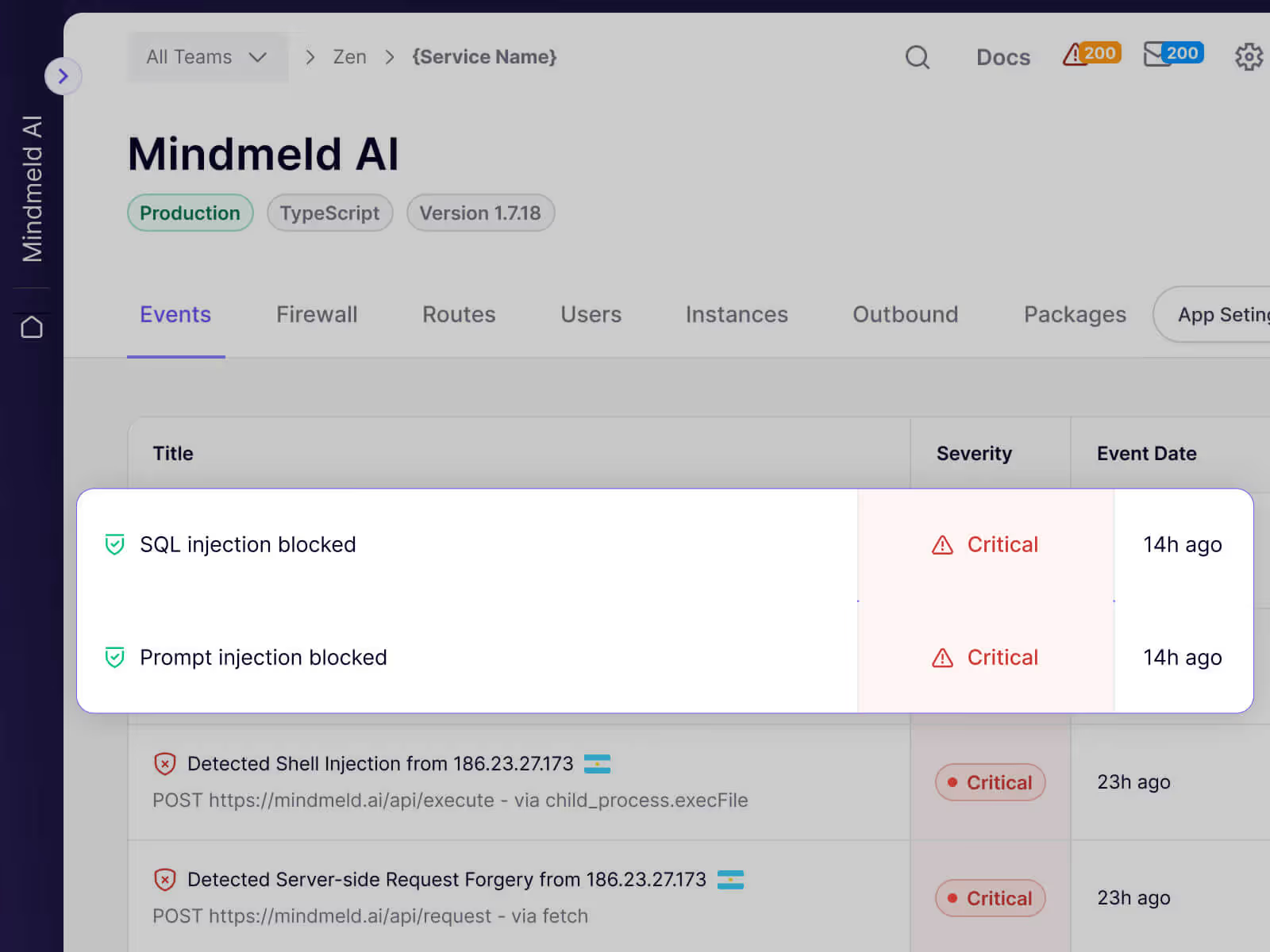
Runtime Protection
Zen is your in-app firewall for peace of mind. Auto block critical injection attacks, introduce API rate limiting & more

Replaces
Code Quality
Ship clean code faster with AI code review. Automatically review code for bug risks, anti-patterns, and quality issues.

Replaces


Secrets detection
Checks your code for leaked and exposed API keys, passwords, certificates, encryption keys, etc...

Replaces


Bug Bounty Validation
Validate, triage, and fix bug bounty reports automatically.

Replaces

Features

We prioritize alerts so you don’t have to.
Deduplication
Related alerts are grouped together, so you can resolve more issues with less effort.
AutoTriage
Aikido evaluates alerts in the context of your code and infrastructure and deprioritizes issues that do not pose real risk to your application.
Custom Rules
Fine tune what is relevant for your team. Exclude specific paths, packages, or conditions while still being alerted when something critical happens.

We help you go from alert to fix.
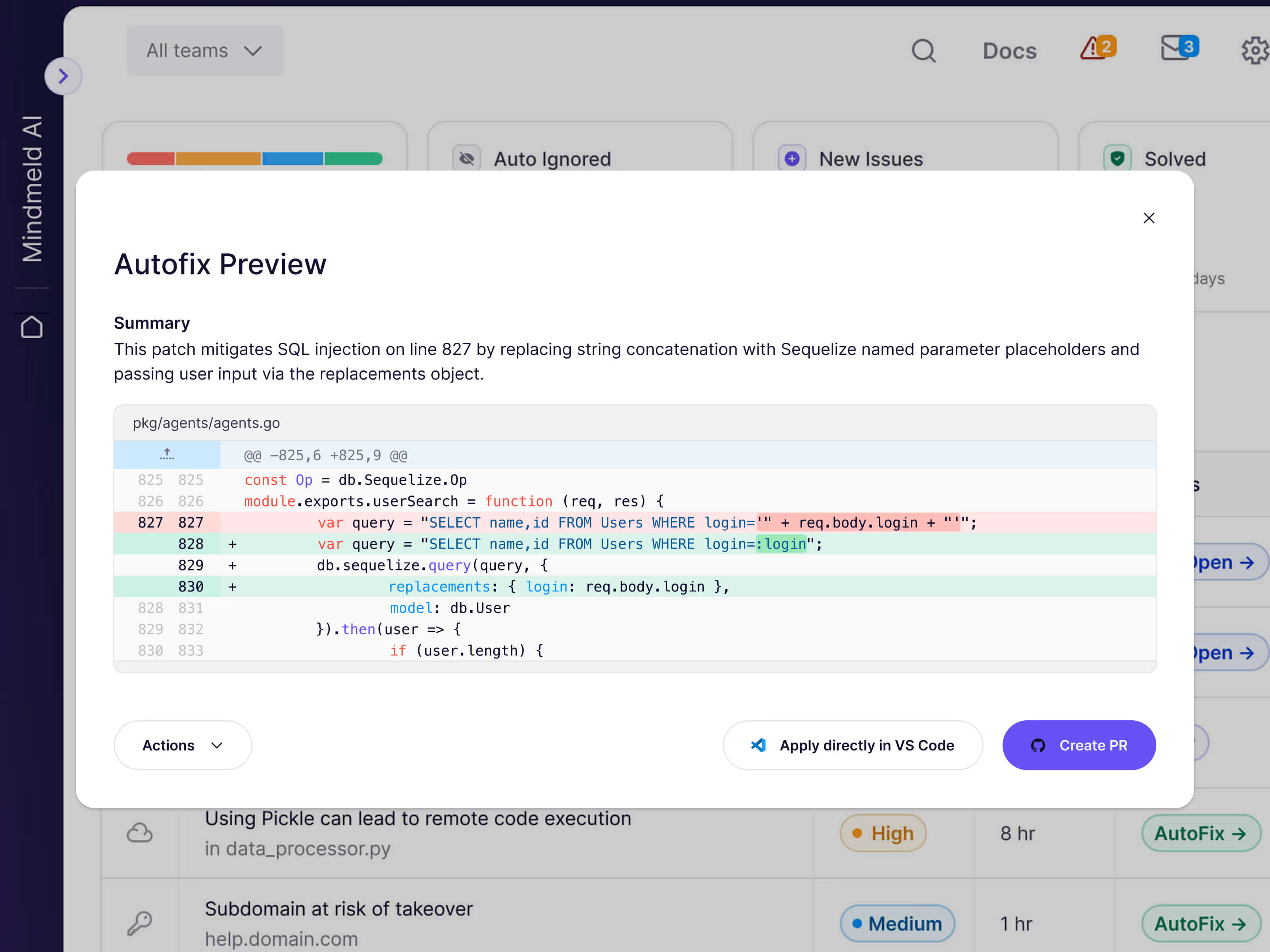
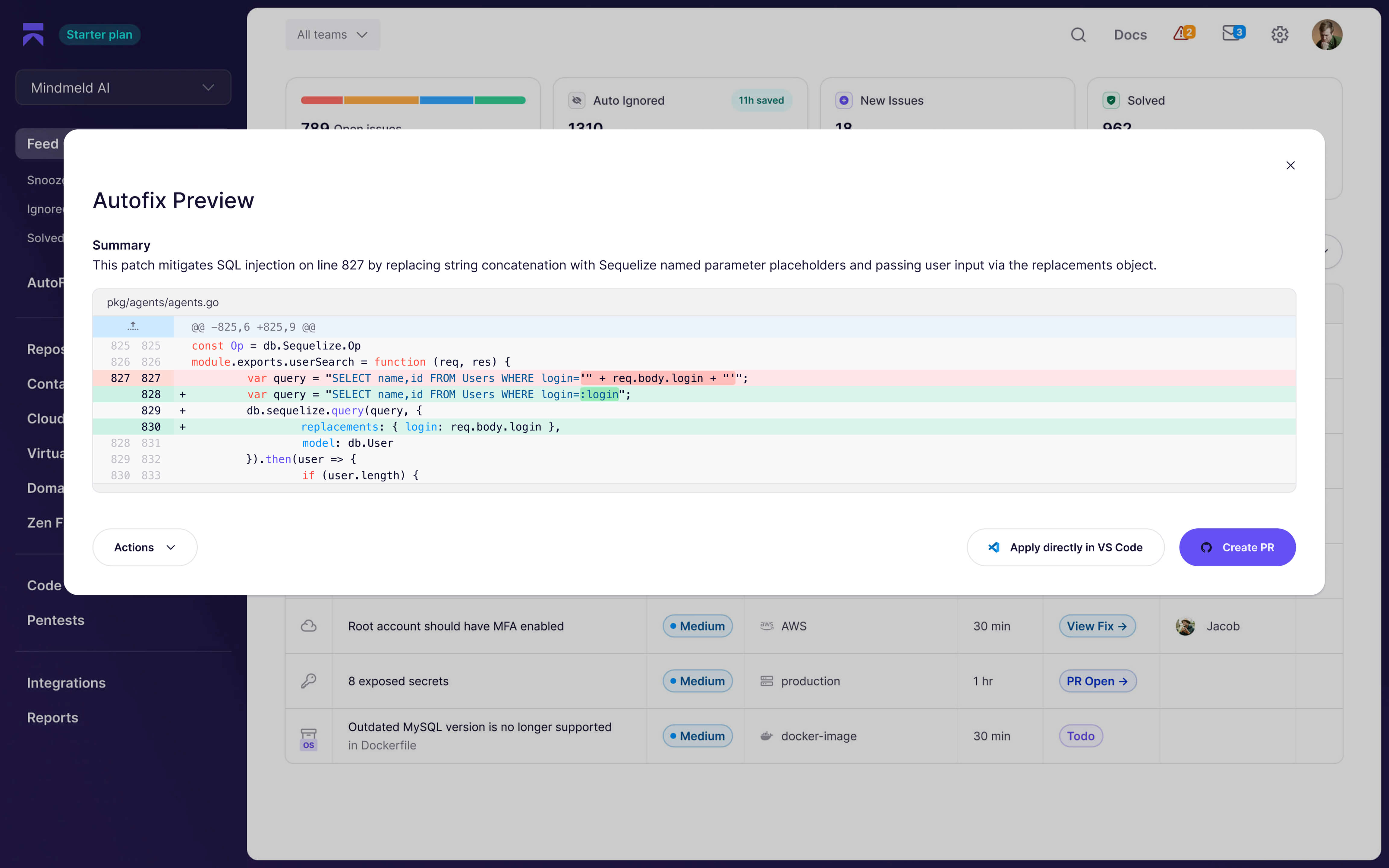
AutoFix
Generate reviewable pull requests to fix issues across code, dependencies, infrastructure, and containers, with full visibility before you merge.
Bulk Fix with One Click
Create ready to merge pull requests that address multiple related alerts at once, saving time and manual work.
TL;DR Summaries
Get a short, actionable summary of what’s wrong and how to fix it. Turn it into a ticket or assign it in one click.
Choose the repos yourself

When you log in with your version control system (VCS) we don’t get access to any of your repositories. You can manually give read-only access to the repositories you’d like to scan.
Read-only access

We can’t change any of your code.
No keys on our side

You log in with your Github, Gitlab or Bitbucket account so we can’t store/view keys.
Short-lived access tokens

Can only be generated with a certificate, stored in AWS secrets manager.
Separate docker container

Every scan generates a separate docker container which gets hard-deleted right after analysis is done.
Data won’t be shared - ever!


The flow must go on
We'll notify you when it's important.














































































Frequently Asked Q's
How does Aikido know which alerts are relevant?
We’ve built a rule engine that takes the context of your environment into account. This allows us to easily adapt the criticality score for your environment & filter out false positives. If we’re not sure, the algorithm always reverts to the safest option...
What happens to my data?
We clone the repositories inside of temporary environments (such as docker containers unique to you). Those containers are disposed of, after analysis. The duration of the test and scans themselves take about 1-5 mins. All the clones and containers are then auto-removed after that, always, every time, for every customer.
Does Aikido make changes to my codebase?
We can’t & won’t, this is guaranteed by read-only access.
I don’t want to connect my repository. Can I try it with a test account?
Of course! When you sign up with your git, don’t give access to any repo & select the demo repo instead!
How is Aikido different?
Aikido combines features from lots of different platforms in one. By bringing together multiple tools in one platform, we’re able to contextualize vulnerabilities, filter out false positives and reduce noise by 95%.
How can I trust Aikido?
We’re doing everything we can to be fully secure & compliant. Aikido has been examined to attest that its system and the suitability of the design of controls meets the AICPA's SOC 2 Type II & ISO 27001:2022 requirements.
Get secure now
Secure your code, cloud, and runtime in one central system.
Find and fix vulnerabilities fast automatically.



















.jpg)
.svg)



.png)











.png)



-1.png)








.png)

.png)








.png)












.png)
.png)


























.png)