Review
“Aikido supports a crucial aspect of our FDA compliance. Its combined code scanning and cloud security features help ensure our medical devices meet necessary software security”

Jonathan V, Security Engineer at Xeos Medical

The FDA, among other instances, require MedTech companies to comply with a whole bunch of cybersecurity regulations. Whether you have a medical app or create medical devices - a security breach can lead to compromised data or malfunctioning of the device, posing users to safety risks. It's essential to be aware and protect your apps & devices against any vulnerability.
Compliance
Aikido performs checks and generates evidence for technical controls for ISO 27001:2022 & SOC 2 Type 2. Automating technical controls is a big step-up towards achieving ISO & SOC 2 compliance.
This globally recognized standard ensures that you systematically identify, assess, and mitigate risks to your information assets while complying with legal requirements. Aikido automates a variety of technical controls.

SOC 2 is a procedure that ensures your service providers securely manage your data to protect the interests of your organization and the privacy of its clients. Aikido automates all technical controls, making the compliancy process much easier.

Organizations in MedTech that create, access, store or exchange sensitive information should use the HITRUST & HIPAA frameworks to ensure that data is safely & securely kept. Aikido will help you with many of these security checks. (SAST & DAST, SCA among other things).

Features
Technical vulnerability management (ISO & SOC2 compliance) is just the start. FDA regulations require all-round cybersecurity protection. Aikido combines dependency scanning (SCA), SAST, DAST, IaC, container scanning, secrets detection, open source license scanning and more.
See our features



Scans your source code for security vulnerabilities such as SQL injection, XSS, buffer overflows and other security risks. Checks against popular CVE databases. It works out-of-the-box and supports all major languages.
Learn more

Dynamic Application Security Testing (DAST) for internet-connected medical devices involves identifying and mitigating vulnerabilities throughout the device's lifecycle. Aikido does continuous monitoring and regular scans post-deployment ensuring the safety of your devices and helping you attain regulatory compliance. Includes API Security.

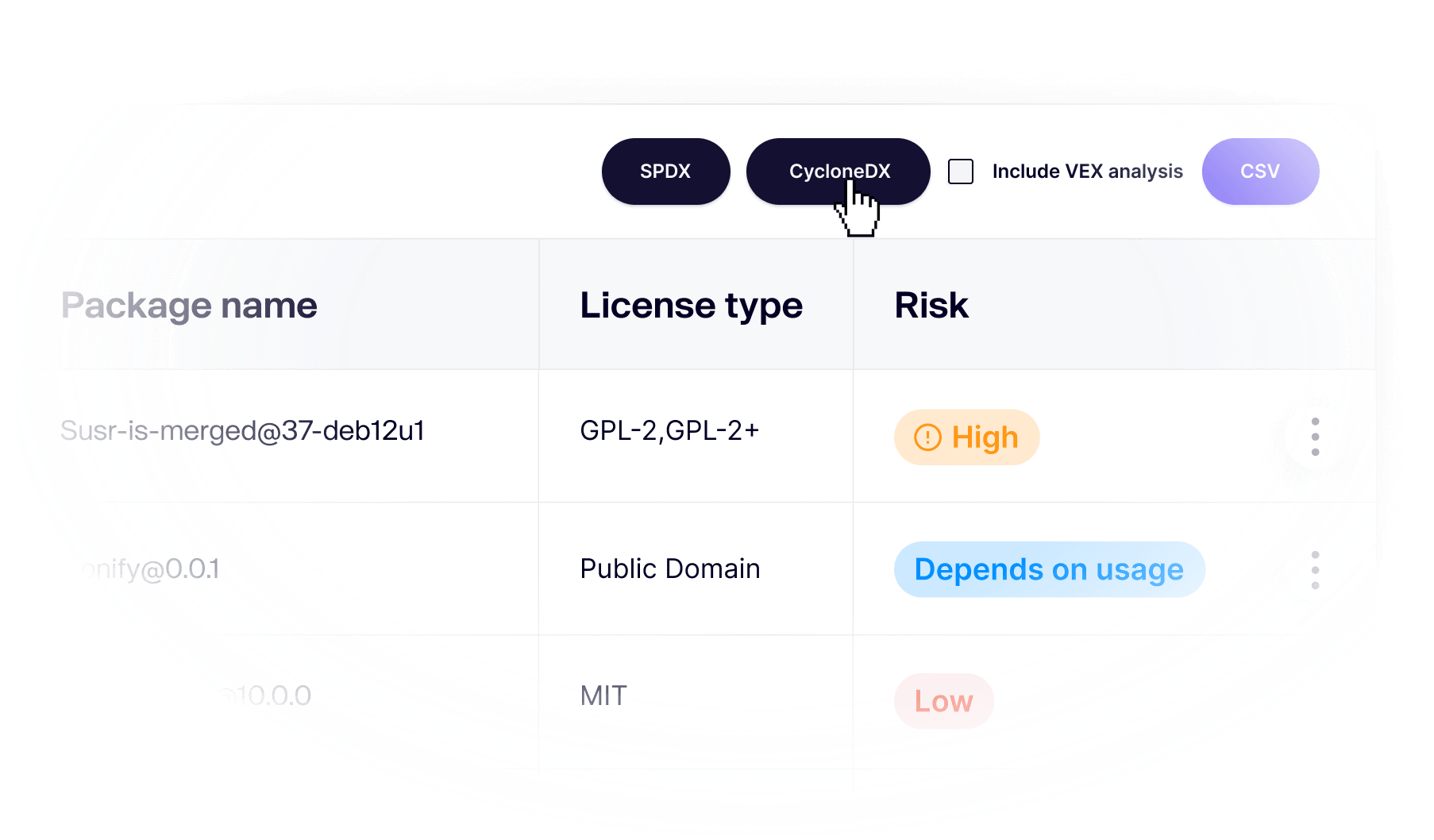
FDA regulations and security audits require you to provide regular SBOMs. Aikido makes it easy to analyse the list of licenses in advance & generate an SBOM whenever you need it.
Scan your container operating system for packages with security issues.
Learn more



The npm ecosystem is susceptible to malicious packages being published because of its open nature.
Aikido identifies malicious code that may be embedded within JavaScript files or npm packages. Powered by Phylum. (Scans for backdoors, trojans, keyloggers, XSS, cryptojacking scripts and more.)
Read more

Analyse third-party components such as libraries, frameworks, and dependencies for vulnerabilities. Aikido does reachability analysis, triages to filter out false positives, and provides clear remediation advice. Auto-fix vulnerabilities with one click.
Learn more



Scans Terraform, CloudFormation & Kubernetes Helm charts for misconfigurations.
Detect cloud infrastructure risks across major cloud providers.


Check your code for leaked and exposed API keys, passwords, certificates, encryption keys, etc…
Our AI agents analyze your code and deployed web apps or APIs, simulate real attacker behavior, and deliver a verified SOC2- and ISO27001-ready report - all within hours.
Integrations
Are you using a compliance suite? Aikido integrates with the suite of your choice.
See our integrations


The fastest path to compliance. It collects 90% of the evidence needed for your certification.

Automates your compliance journey from start to audit-ready and beyond.

Sprinto is a one-stop platform for all security compliances and certification audits.
Thoropass is an end-to-end compliance solution offering a seamless security audit experience.
Leading security compliance automation platform that makes getting any compliance fast & easy.
SOC 2 Controls
CC3.3: Consider the potential for fraud
CC3.2: Estimate Significance of Risks Identified
CC5.2: The entity selects and develops general control activities over technology to support the achievement of objectives
CC6.1
CC6.6
CC6.7
CC6.8
CC7.1: Monitor infrastructure and software
CC7.1: Implement change detection mechanism
CC7.1: Detect unknown or unauthorized components
CC7.1: Conduct vulnerability scans
CC7.1: Implement filters to analyze anomalies
CC7.1: Restores the affected environments
CC10.3: Tests integrity and completeness of backup data
CC8.1: Protect confidential information
CC8.1: Track system changes
ISO 27001 Controls
A.8.2: Privileged access rights
A.8.3: Information access restriction
A.8.5: Secure authentication
A.8.6: Capacity management
A.8.7: Protection against malware
A.8.8: Management of technical vulnerabilities
A.8.9: Configuration management
A.8.12: Data leakage prevention
A.8.13: Backups
A.8.15: Logging
A.8.16: Monitoring activities
A.8.18: Use of privileged utility programs
A.8.20: Network security
A.8.24: Use of cryptography
A.8.25: Secure development lifecycle
A.8.28: Secure coding
A.8.31: Separation of development, test and production environments
A.8.32: Change management
A.5.15: Access control
A.5.16: Identity management
A.5.28: Collection of evidence
A.5.33: Protection of records
Review

Jonathan V, Security Engineer at Xeos Medical
Yes — we run yearly third-party pentests and maintain a continuous bug bounty program to catch issues early.
No! Unlike others, we're fully API based, no agents are needed to deploy Aikido! This way you're up & running in mere minutes & we're way less intrusive!
Of course! When you sign up with your git, don’t give access to any repo & select the demo repo instead!
We clone the repositories inside of temporary environments (such as docker containers unique to you). Those containers are disposed of, after analysis. The duration of the test and scans themselves take about 1-5 mins. All the clones and containers are then auto-removed after that, always, every time, for every customer.
Secure your code, cloud, and runtime in one central system.
Find and fix vulnerabilities fast automatically.

