The all-in-one Veracode alternative
Secure your code, cloud, and runtime in one central system. Find and fix vulnerabilities automatically.
.avif)


.png)






























How Aikido compares to Veracode
Aikido offers flat, transparent fees with no hidden charges. Veracode is modular and can get expensive if you require multiple scanning features.
Modular pricing





- Reachability Analysis
- Malware Detection in Dependencies
- AutoFix for SCA
- License Compliance
- SBOM Support
- License PR Release Gating
- Noise Reduction (False Positive Filtering)
- More Noisy



- SAST AI Autofix
- Multi-file Analysis
- Taint Analysis
- Custom SAST Rules
- SAST Directly In IDE



- API Discovery/API Fuzz Testing
- Authenticated DAST
- Automated Swagger Creation
- Attack Surface Monitoring
- Only API Scanning


- Whitebox, Greybox, Blackbox Pentests
- IDOR Detection
- Compliance PDF Reports (ISO27001, SOC2)


- Infrastructure as Code Scanning
- Cloud and K8s Posture management
- Virtual Machine Scanning
- Attack Path Analysis
- Cloud Search



- Extended Lifetime Support
- AI AutoFix For Container Images
- Malware Detection in Containers








How users rate us
Based on user reviews.


Everything You Wish Security Tools Actually Did
Static Application Security Testing (SAST)
Scans your source code for security vulnerabilities such as SQL injection, XSS, buffer overflows and other security risks. Checks against popular CVE databases. It works out-of-the-box and supports all major languages.

Software Composition Analysis
Analyse third-party components such as libraries, frameworks, and dependencies for vulnerabilities. Aikido does reachability analysis, triages to filter out false positives, and provides clear remediation advice. Auto-fix vulnerabilities with one click.

Infrastructure as code (IaC)
Scans Terraform, CloudFormation & Kubernetes Helm charts for misconfigurations.
- Catch misconfigurations that expose your infrastructure to risk
- Identify vulnerabilities before they reach your main branch
- Integrates in your CI/CD Pipeline

Container Security
Scan your container operating system for packages with security issues.
- Checks if your containers have any vulnerabilities (Like CVEs)
- Highlights vulnerabilities based on container data sensitivity
- Auto-fix your container images with AI

DAST & API Security
Monitor your app and APIs to find vulnerabilities like SQL injection, XSS, and CSRF, both on the surface and with authenticated DAST.
Simulate real-world attacks and scan every API endpoint for common security threats.
.avif)
Cloud & K8s Security Posture Management (CSPM)
Detect cloud infrastructure risks across major cloud providers.
- Scans Virtual Machines (AWS EC2 instances) for vulnerabilities.
- Scan your cloud for misconfigurations and overly permissive user roles/access
- Automate security policies & compliance checks for SOC2, ISO27001, CIS & NIS2

Secrets detection
Check your code for leaked and exposed API keys, passwords, certificates, encryption keys, etc…

Malware detection
The npm ecosystem is susceptible to malicious packages being published because of its open nature. Aikido identifies malicious code that may be embedded within JavaScript files or npm packages. (Scans for backdoors, trojans, keyloggers, XSS, cryptojacking scripts and more.)

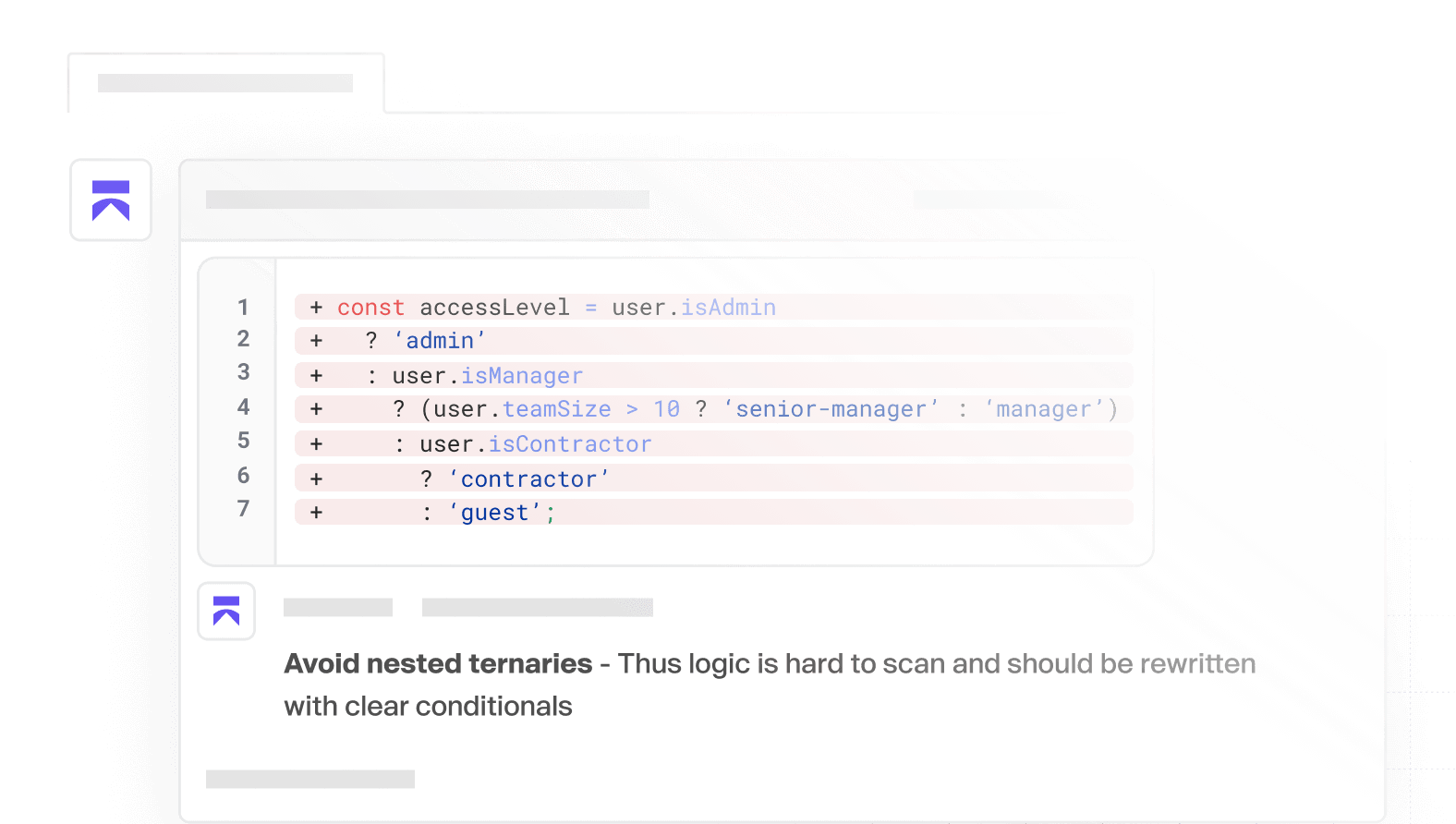
AI Code Quality
Ship quality code, faster. Instant feedback, smart detection, and clear PR comments, so you can focus on building.
Get secure now
Secure your code, cloud, and runtime in one central system.
Find and fix vulnerabilities fast automatically.


Migrating to Aikido
This is the migration hub for teams replacing an incumbent code, cloud, or supply-chain security tool with Aikido. The safe pattern is phased: onboard assets, preserve evidence, route ownership, run in parallel, then move enforcement one capability at a time.
Who this is for
Security leads, platform engineers, and CTOs migrating any incumbent code, cloud, or supply-chain scanner to Aikido. That includes teams replacing older SAST programs, point tools, or multi-tool stacks and wanting one rollout pattern that works across repositories, cloud accounts, container registries, and related scanning surfaces.
The migration pattern in one paragraph
Aikido migrations are usually run as a phased overlap, not a freeze-and-cutover event. Start with visibility, keep one tool as the blocker while the other measures, baseline historic debt so only net-new issues drive enforcement, make sure every onboarded asset has an owner, preserve legacy evidence in read-only form during the overlap, and cut over by capability or category rather than by one big-bang retirement date.
The migration playbook (any path)
Visibility first, blocking later
Connect the assets you want to migrate first, confirm coverage, and let teams see findings before you enforce on them. The early goal is signal quality, ownership, and workflow fit — not day-one blocking.
Parallel run: one tool blocks, the other measures
During overlap, avoid double-blocking. Keep the incumbent tool as the active blocker for a capability while Aikido runs in measurement or warn-only mode, then swap roles when you are ready to cut over. One tool blocks; the other measures.
Baseline historic debt vs net-new
Treat historic findings as baseline debt and keep enforcement focused on net-new issues. That gives teams a clean starting point and avoids turning migration week into a backlog reset project.
Ownership and smart issue routing
Do not onboard a repo, cloud account, registry, or app surface without an owner. Before enforcement, set teams, CODEOWNERS, any path-based assignment you plan to use, and Jira smart routing so new findings land with the right team from day one.
Audit and evidence continuity
Keep the old tool's evidence read-only during the overlap for audit continuity. For ongoing evidence in Aikido, use the Security Audit Report and the available export and integration surfaces: PDF report export, issue export, activity log API, SBOM and VEX export, REST API, webhooks, and Vanta integration.
Cutover and decommission criteria
Cut over by capability or category, not by one calendar date. For example, move one category at a time from report-only to enforcement, confirm routing and evidence collection are working, then decommission the incumbent tool for that category. Full retirement follows once the categories you care about have clean ownership, stable gating, and acceptable evidence coverage.
Vendor-specific migration guides
- Migrating from Snyk to Aikido — practical guidance for moving from a multi-product developer AppSec stack to Aikido.
- Migrating from SonarQube to Aikido — guidance for teams moving from code-quality and SAST-led workflows to broader coverage in Aikido.
- Migrating from Semgrep to Aikido — guidance for teams replacing custom-rule-heavy SAST workflows with Aikido.
- Migrating from Checkmarx to Aikido — guidance for replacing a legacy SAST rollout with a lower-friction transition path.
- Migrating from Veracode to Aikido — guidance for moving from scan-cycle-driven AppSec to a continuous Aikido rollout.
Onboarding surfaces
Aikido onboards across source code management systems, cloud accounts, container registries, and, where documented, DAST / Surface Monitoring app domains. Before enforcement, configure teams, CODEOWNERS and assignment rules, roles and permissions, task-tracker routing, and SAML / SSO so the rollout model is already in place when blocking begins.

