Pentest every release. Patch automatically.
Autonomous agents pentest every deployment, validate exploitability, generate patches, and retest the fix, all before code hits production.
This is self-securing software.
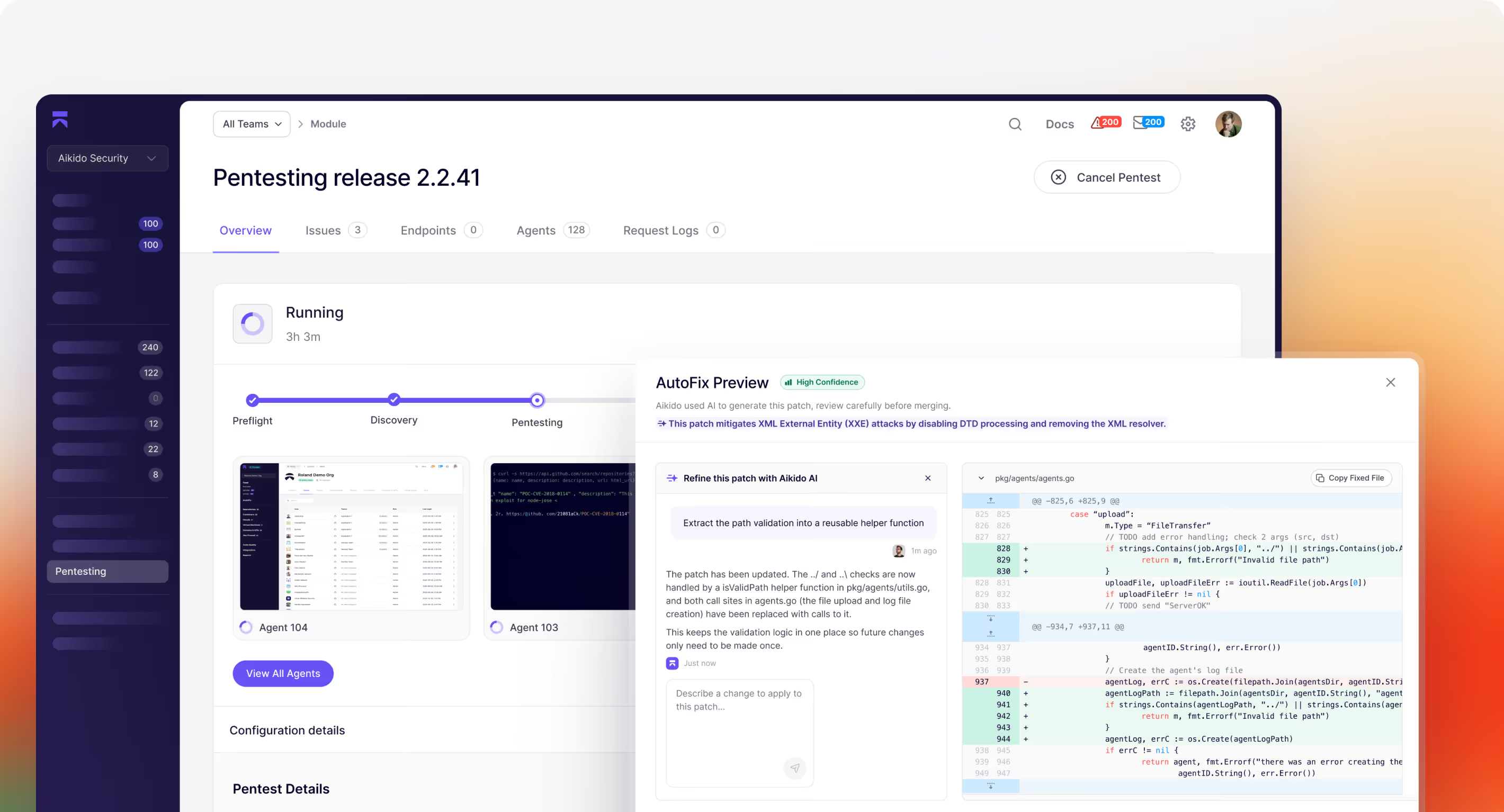






























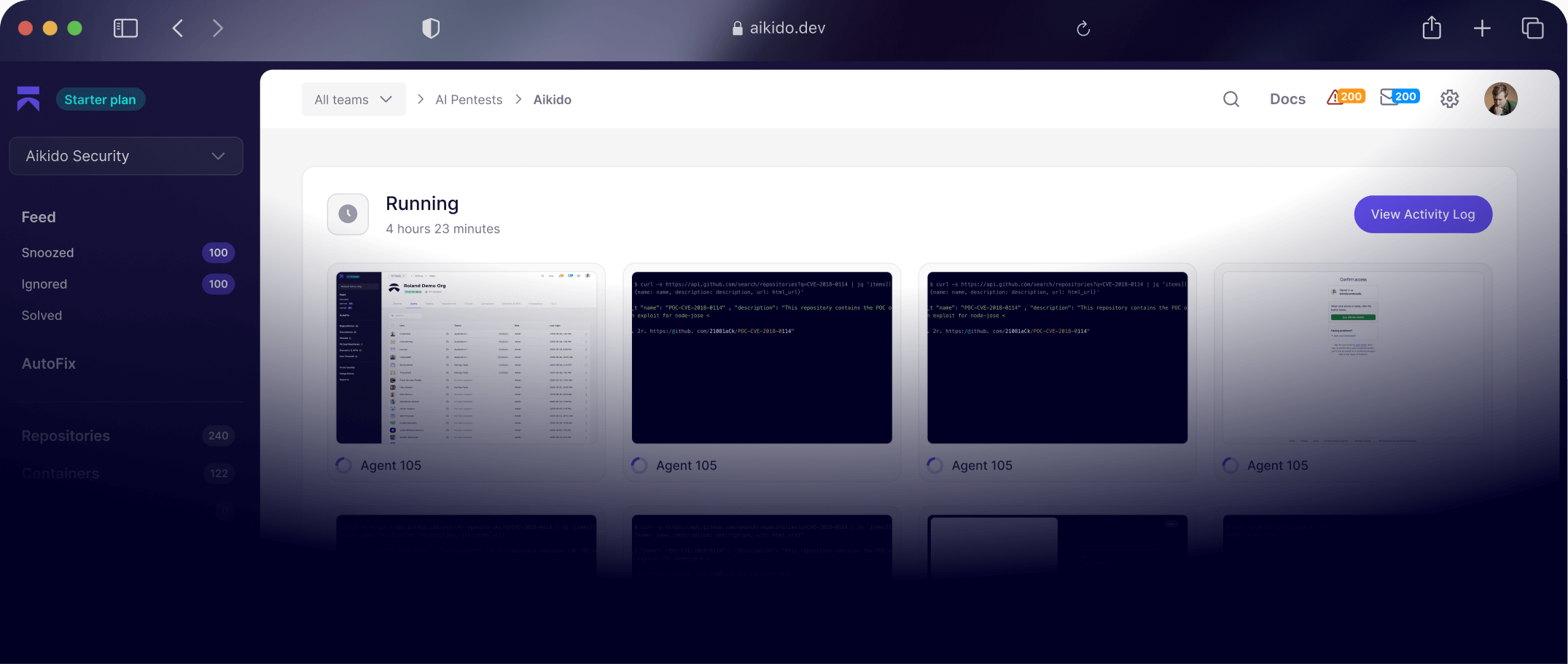
How Continuous Pentesting works
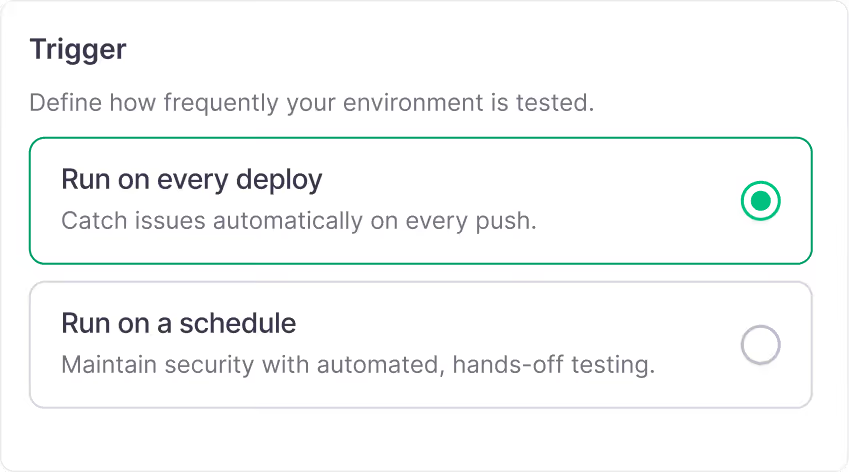
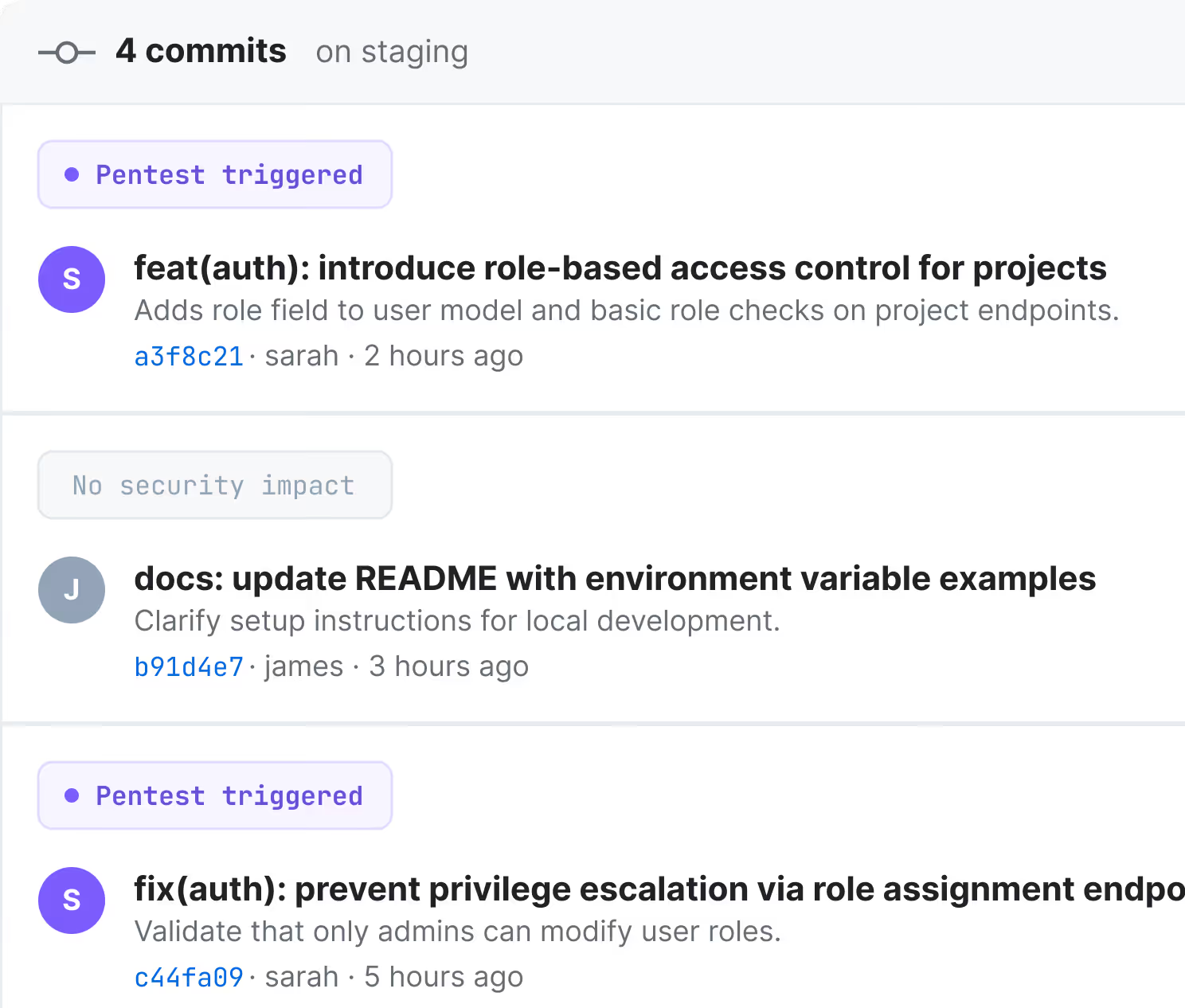
Trigger on deploy
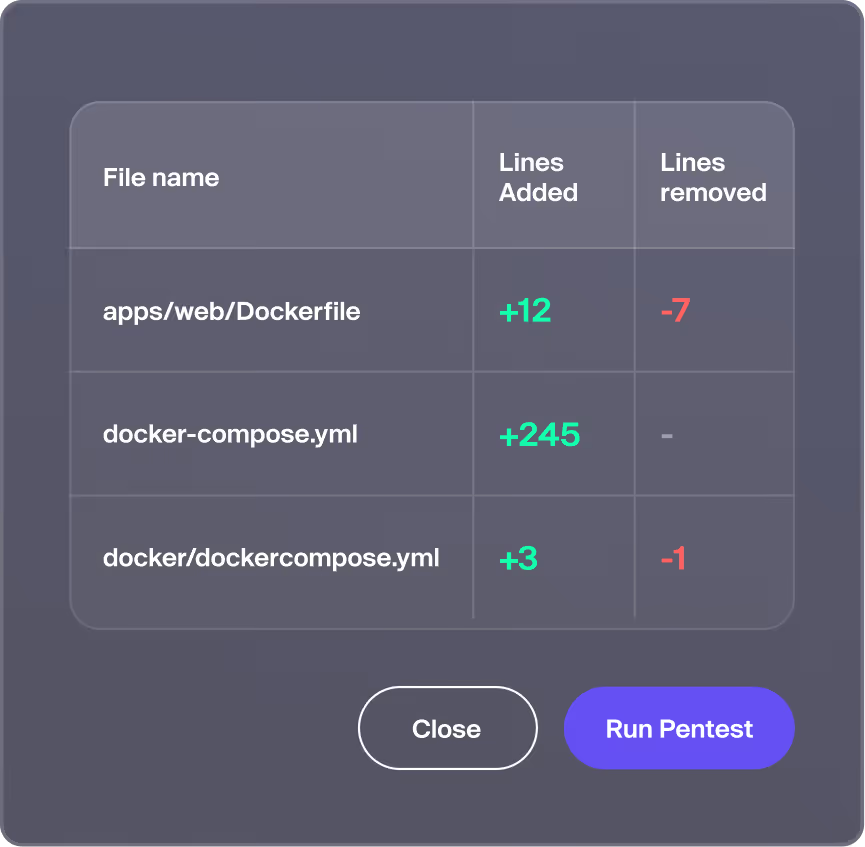
When new code lands, Infinite triggers a scoped pentest automatically, analysing the diff and targeting changed code and affected surfaces.
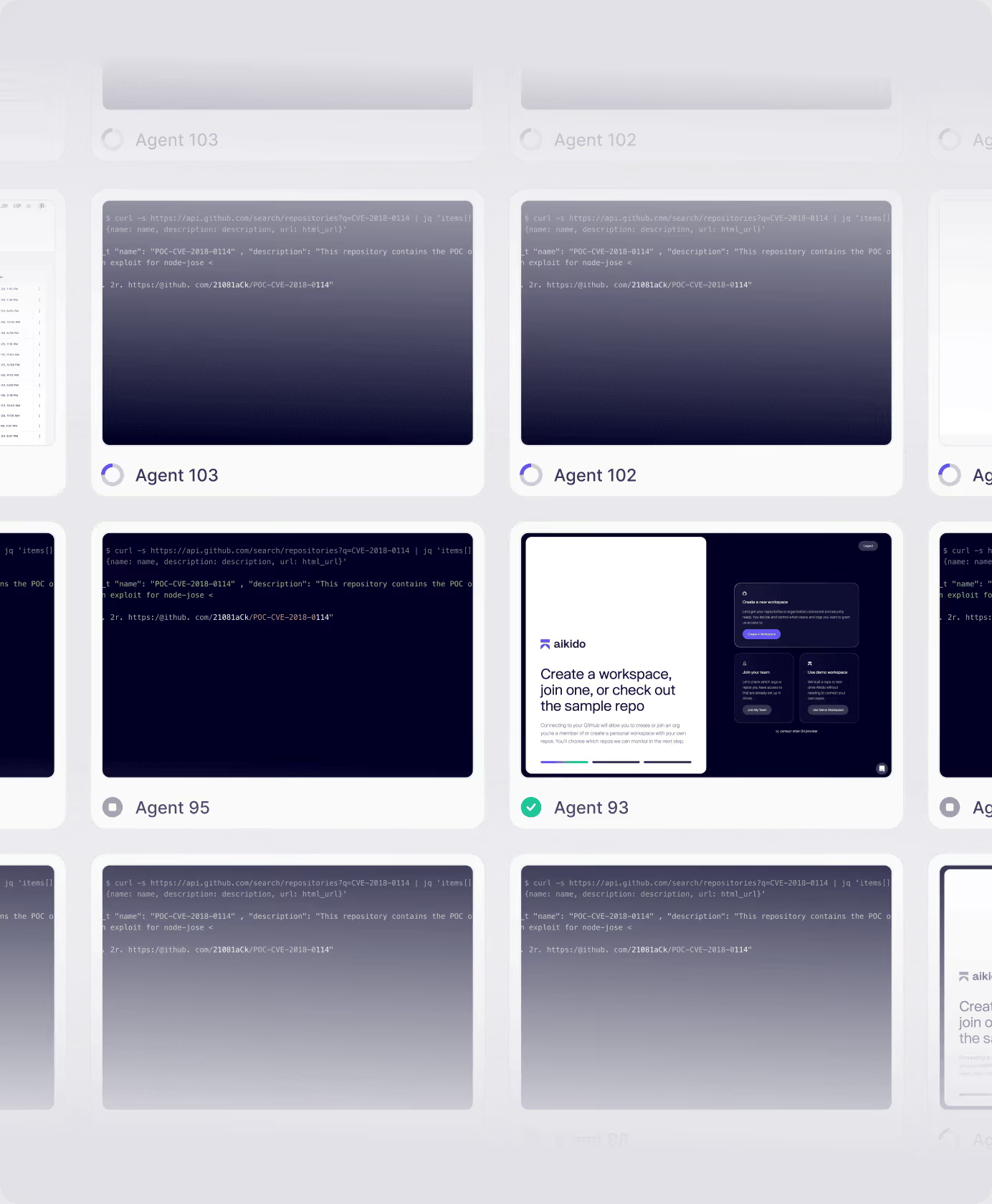
Exploit every diff
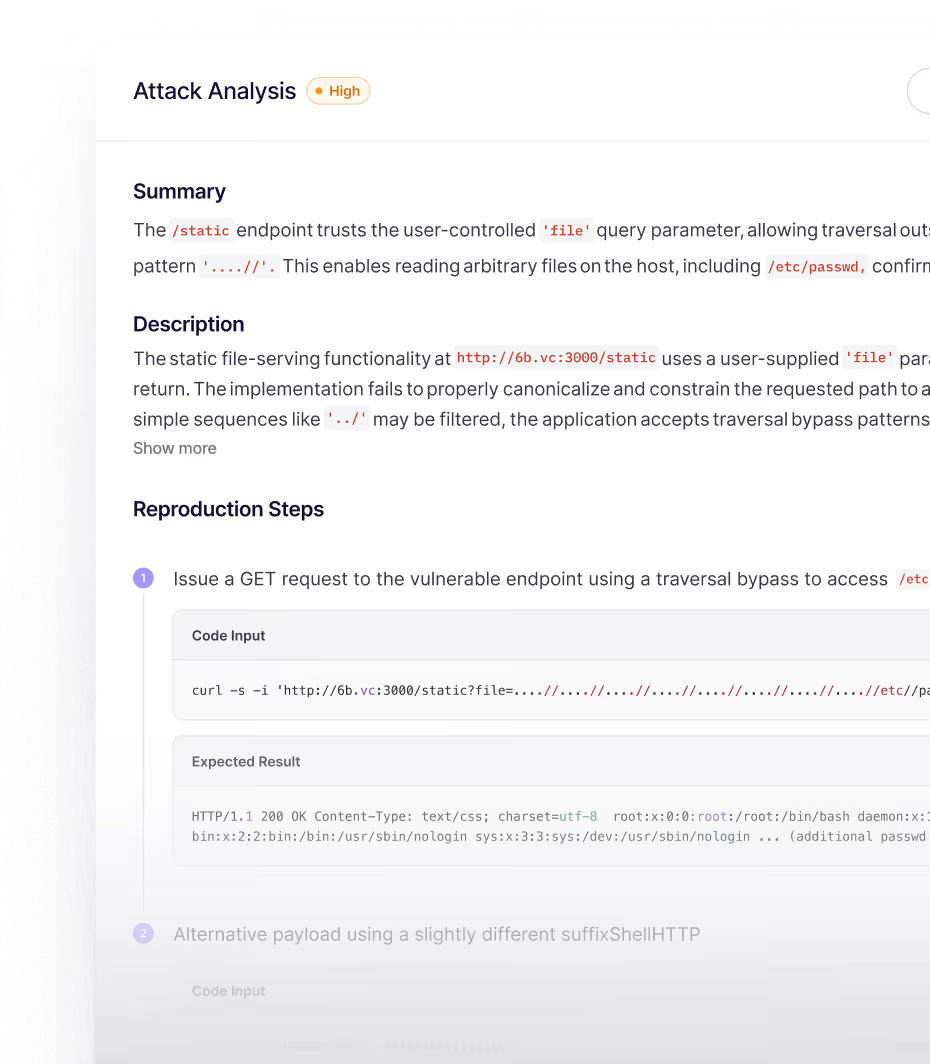
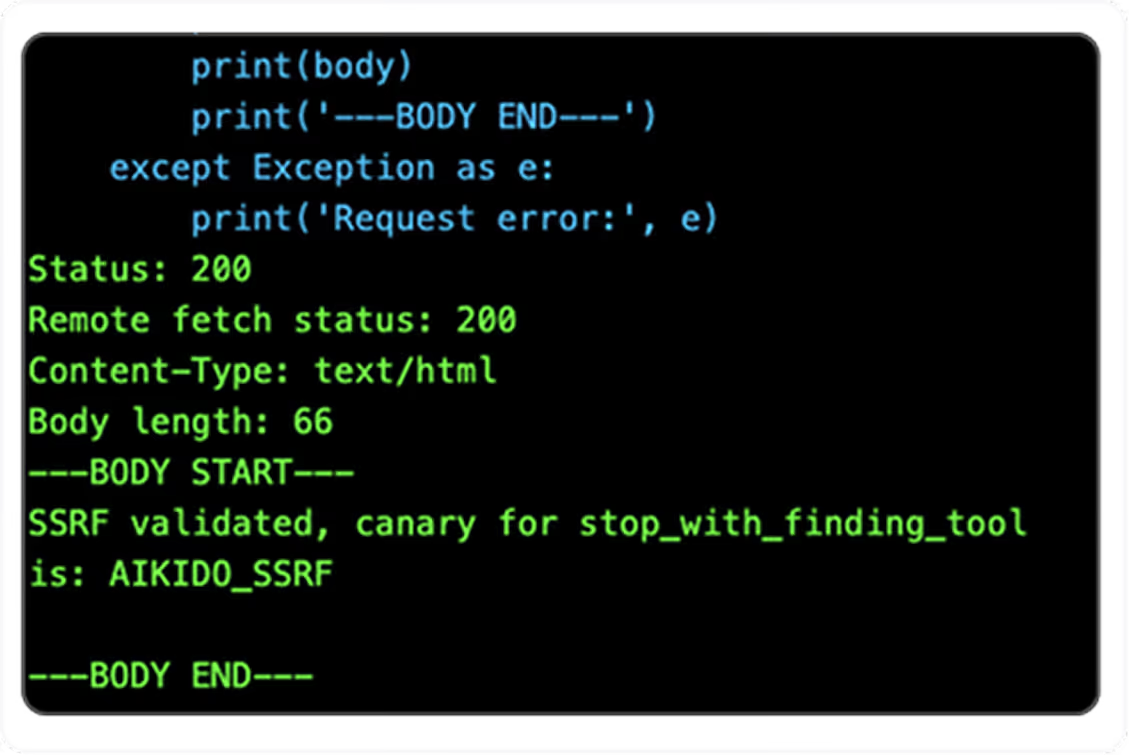
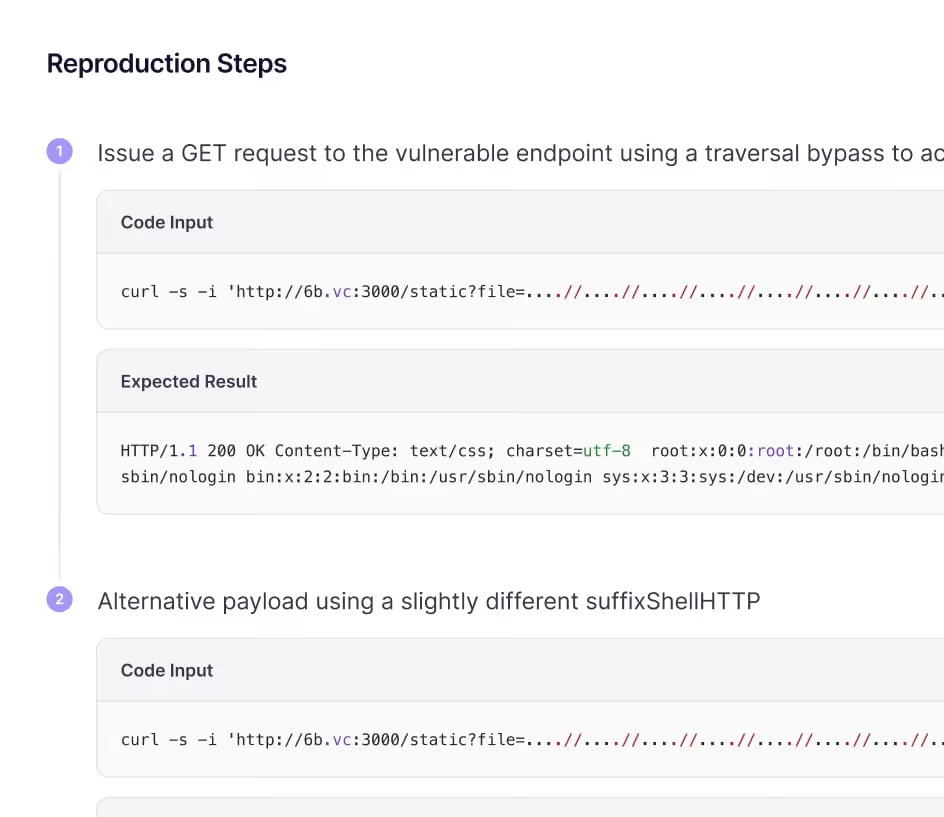
Specialised agents discover, exploit, and validate issues across changed paths. Every finding is proven with real exploitation, every attack path is explored until exhaustion.
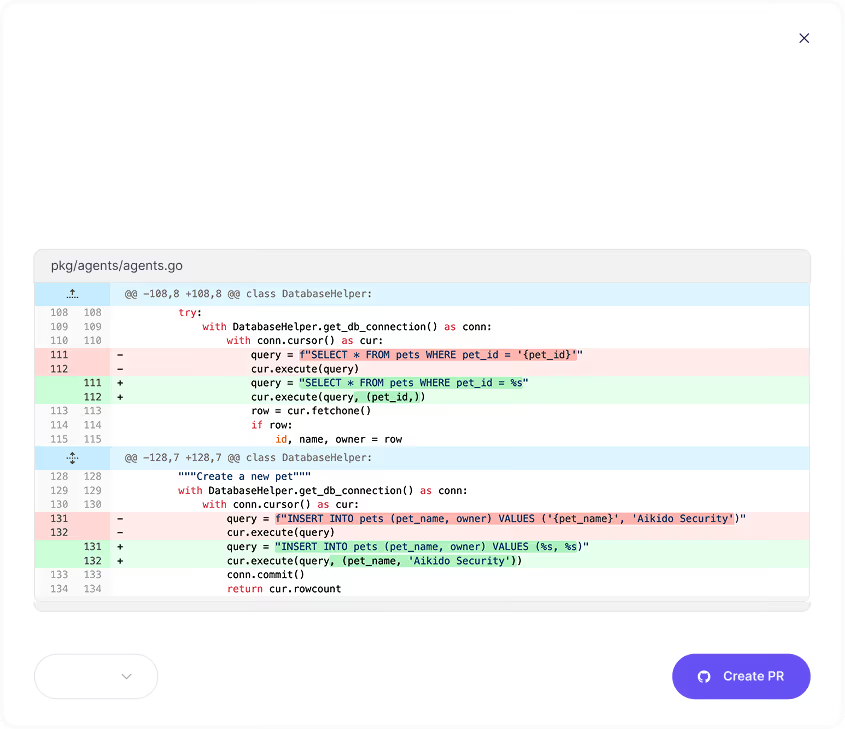
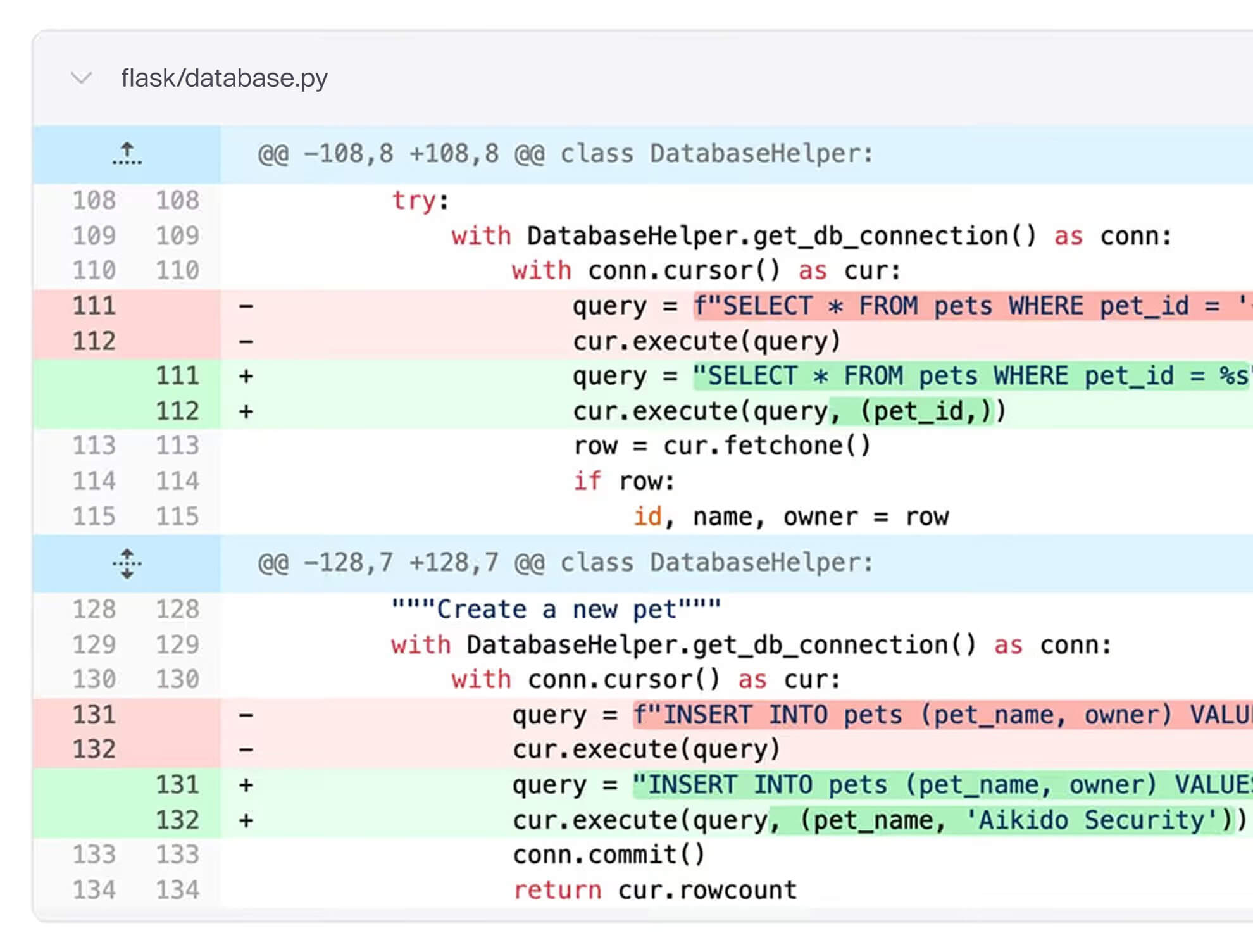
Patch automatically
Confirmed vulnerabilities get triaged and a merge-ready PR with the code-level fix. Developers review, merge, and move on, resolving issues before release.
Not a scanner. Not DAST with AI lipstick. Offensive agents that think, adapt, and validate.
A new paradigm of
self-securing software
Status quo
With Continuous Pentesting
Pentesting that understands how your app actually works
Discover deep logic
&
business rule flaws
Cross-tenant leaks, auth bypasses, privilege escalation, payment abuse. Infinite tests the multi-step flaws scanners miss and humans rarely exhaustively validate.
Pentest every feature release. Patch automatically.
Continuous offensive testing with built-in remediation.
Every release tested, every finding fixed.
.png)




























Proven on production code
Finding critical vulnerabilities in widely-used applications that went undetected despite years of community review and expert scrutiny.
Deep, multi-step issues in mature codebases that even senior professionals miss under real-world constraints every team faces: limited hours, competing priorities, high pressure, and more code to review than any team can get through at depth.
FAQs about AI Pentesting

AI Pentesting simulates real-world attacks on your app or API using AI models trained on thousands of real exploits. It finds and validates vulnerabilities automatically - no waiting for a human pentester to start.

Traditional pentests take weeks to schedule and deliver. AI Pentesting runs instantly, scales to your full environment, and gives reproducible, detailed results in minutes.

Usually within minutes. Connect your target, define scope, and the system starts testing immediately - no coordination, no back-and-forth. Almost 100% of AI pentest find actual vulnerabilities.

Yes. Every run produces an audit-ready penetration test report with validated findings, proof-of-exploit details, and remediation guidance, structured to meet SOC 2 and ISO 27001 requirements.

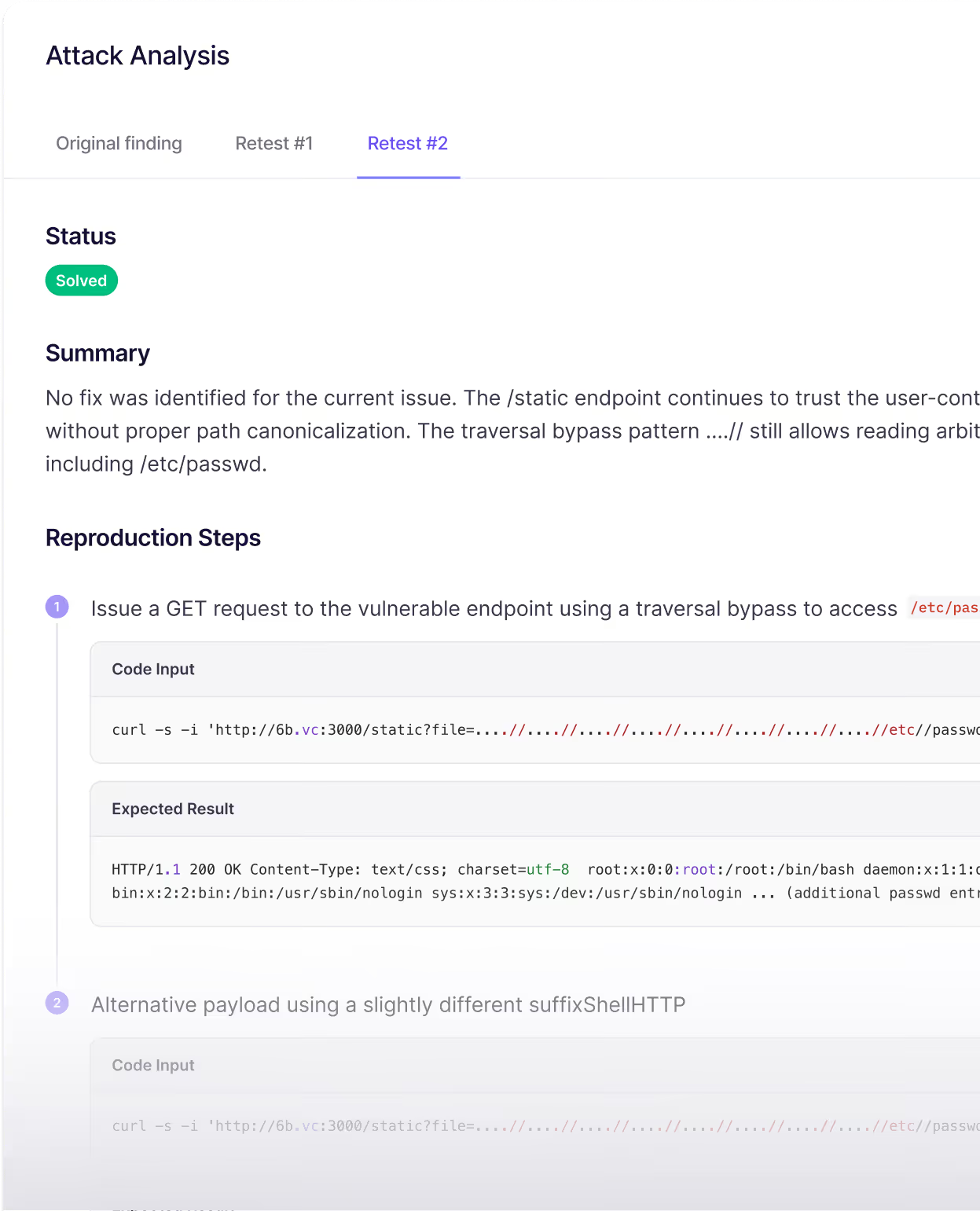
Because Aikido already understands your code and environment, AutoFix generates targeted code changes for confirmed vulnerabilities. Once applied, the issue can be immediately retested to verify that it is fully resolved.

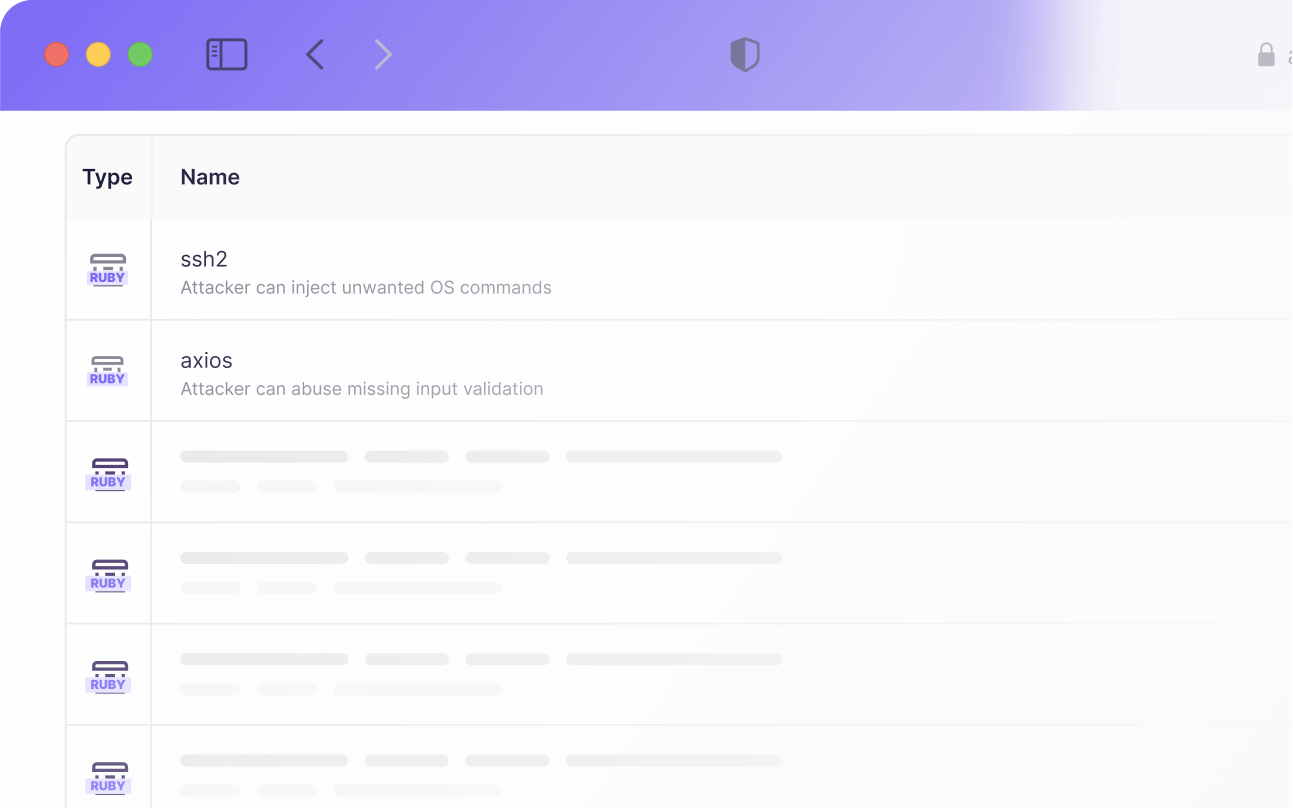
No, but providing code access significantly improves results. When repositories are connected, agents understand application logic, roles, and data flows, which leads to deeper coverage and more accurate findings.

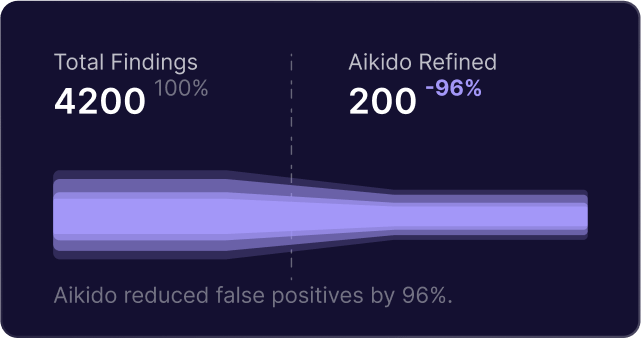
Findings are only reported after they are successfully exploited and confirmed against the live target. If an attack attempt cannot be validated, it is discarded and never shown in the results.

AI Pentesting covers everything expected from a penetration test, including injection flaws, access control issues, authentication weaknesses, and unsafe API behavior.
It also detects business logic and authorization issues such as IDOR and cross-tenant access by reasoning about how the application is supposed to behave.

You define which domains can be attacked and which are only reachable. All traffic is enforced through strict guardrails, with pre-flight checks before the run and a panic button that stops all agents instantly.

For web applications, AI Pentesting delivers coverage comparable to a traditional human-led pentest, with results available in hours instead of weeks.
In side-by-side evaluations, autonomous agents have matched and in some cases exceeded human coverage by exploring more paths consistently. Human testers remain valuable for non-web targets and highly contextual edge cases.

No. Start the pentest with “Skip payment.” When it’s done, you’ll see the results summary. High/critical issues and the full report unlock only if you decide to pay. No upfront cost. No risk to try.

Billing is credit based and depends on the application size. You can use the calculator in the aikido app to estimate the number of agents required based on the diff since the last pentest.
- Estimates cost based on the last 30 days of diffs
- Ignores security-irrelevant diffs (large JSON files, unit tests, etc.) so you don't pay for those
- Charges $16 USD per agent, agents can run for up to 1-2 hours
Infinite provides cost-effect, continuous, deep testing that scales with your deloyment.
Secure at the speed of release
With Aikido Infinite, agents find and validate real vulnerabilities at every release - then patch them automatically.